Monitoring & Response:
A key aspect of your cyber assurance strategy that for many organisations has been around for years, but a strategy that has never really been addressed, or even acknowledged previously as a problem.
However, the recognition that cyber-attacks and breaches could now happen to anyone, is inevitably bringing the consideration of ‘situational awareness’ to the top of the pile.
- But what do you need from a monitoring & logging solution?
- What should a Security Operations Centre (SOC) provide for you?
- How can you both demonstrate the value and return of your business?
- Can you be assured that your environment is monitored for the wide range of threat actors, types of attacks and level of sophistication that may be deployed against you?
The SOC (Security Operation Centre) is the centralised hub for organisational logging and monitoring which can either be in-house or outsourced to provide visibility over technical and security issues. Having a SOC is key to understanding your organisational security posture in order to prevent and protect key assets.
We are going to explore some of these issues in a series of blogs. The industry has made a number of attempts to define ‘good’ for this area, but there are as yet no clear standards, expectations or buying help.
This will change, but in the meantime we are going to look at a number of key issues, starting with: Do you need a 24x7 SOC service?
Asking the right questions
Most organisations believe that by simply having a SOC 24 x 7 they have enhanced security and are better protected against threats and vulnerabilities, unfortunately this leads into a false sense of security. At Nettitude, this has been the issue of many debates.
On one hand, having dedicated analysts around the clock watching your environment sounds exactly the sort of thing that is required. After all, cyber-attacks don’t just happen between 9-5 in your particular time zone!
On the other hand, is this the overriding factor that will help you both detect and react to a breach in the best possible manner? What happens if your business is 9-5, who is going to respond at 2 am within your business? How much meaningful investigation will take place at that time? What about the capability of the SOC team? If you only have SIEM/Log analysis, who is going to responsible for the Incident Response?
The reality is that a 24x7 SOC itself is not the primary indicator of success.
The real questions that need to be addressed are ‘how good is your SOC?’, and ‘how can it be measured?’.
A SOC needs to be operating at the best of its ability, maturing well and constantly updating with threat intelligence, to include not just the latest emerging threats but also innovative ways of detecting new threats. A SOC needs to be able to operate at the same level as your adversary. If you are looking to provide assurance that means you can withstand a nation state or organised crime group from successfully attacking you, what capabilities and depth do you need within your SOC and IR teams? Does your SOC even have in-depth IR capability available?
A great SOC is not a standalone department, it needs full interaction with your cyber security assurance programme for optimal results.
Cyber Security Assurance
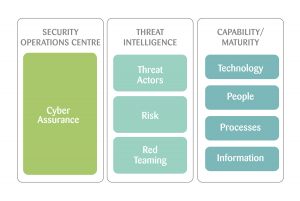
There are many areas that we can dive into, but the main areas that often get discussed are around the capability of a SOC are: Technology, People, Process and Information. To this we would add Threat Intelligence and frame this all in the context of Assurance (i.e. ultimately, confidence that you can detect and effectively deal with a breach when it happens).
The Financial Service sector has implemented the CBEST programme which takes the CREST STAR scheme and applies it to their industry. The foundation of this is the desire to provide a level of assurance to the UK financial services sector that they could manage a sophisticated cyber-attack. The use of threat intelligence, simulated testing and incident response maturity assessments are the key building blocks to achieving this.
Within a SOC, proving that assurance must be a key objective.
So, before we dive into insisting on a 24x7 SOC, let’s look at the real issues that we should be looking for within any SOC service (in house, hybrid or fully outsourced).
Threat Intelligence (TI)
Having accurate TI is crucial when looking at detecting threat actors and activity. One of the first challenges of any monitoring & logging solution is the sheer amount of logs and data you will potentially have to deal with.
There are 3 areas this should help you with:
1. Identifying Threat Actors – Know your enemy! Who they are, but also how they operate and how likely they are to come after you. Threat Intelligence can help you identify quickly your highest priorities in terms of likely attacks to be seen, what assets they may be going after and how they may seek to attack.
2. Context of Risk - This must be understood in the context of risk. Remember your threats are a component of your overall risk, so make sure your SOC knows what your critical assets are, where they are and what vulnerabilities you may have so that they can act in an intelligent manner to help monitor them.
3. Red Teaming – If you really want assurance then you need to simulate the very events you are trying to protect yourself from. Having a Red Team (penetration testing experts) that is integrated with training, and working alongside your SOC is vital. How will you know they will provide the capabilities you need, when you need it, if they have never experienced the right level of attacks?
If the information we base our threat on is incorrect, irrelevant or out-of-date, the chances are the high number of false positives will drown out the real threats. As threats constantly change, it can be hard to keep up and know where to look next.
Poor threat intelligence is essentially looking in the wrong direction which is the equivalent to not looking at all. It’s also an early warning sign: a little like people flashing their headlights at you to indicate an upcoming hazard, or speed camera. Use TI to help you know what is round the corner!
A good SOC must use true Threat Intelligence to inform, shape and define the service provided. This will be done at both the geographical, sector and individual level for each customer.
There are generally 3 ways in which SOC services are provided:
1. You may have/need a fully in-house provided capability including deep dive IR capabilities;
2. You may be looking at an in-house 1st/2nd line capability with an outsourced 3rd line/expert/IR extension, or
3. You may be looking for a fully outsourced model.
There are multiple components that need to be regularly monitored, tweaked, trained, educated and updated when thinking about a beneficial and reliable SOC that go a long way beyond ticking a box to say the SOC you have is 24 x 7.
SOC Maturity
There are then 4 areas that you need to look at within the core capabilities of a SOC that will help you determine if a SOC is good for you.
The SOC maturity is also crucial to the effectiveness and understanding baseline activities and anomalies. The SOC should also have a maturity plan assessing its current state, where it aims to be and how it intends to bridge that gap.
1. Information – All SIEM platforms correlate and take in data from log sources. How these are tuned, which ones are used, how effective they are to detect the type of activity you’re trying to detect, are all important. Incorporating information about the environment (key assets, vulnerabilities, threats, etc) is also key.
2. People - When looking at personnel within the SOC, it is important to recruit based on experience and certification, but also to assess capability. Although it may be tempting to employ graduates for all your roles, you will not gain the depth of experience needed to deal with the potential level of threat you need to monitor for.
What in fact you probably need is an experienced team with a variety of skill sets and experience to be able to address a wide variety of issues and concerns. Members of the team should also support the maturity process by helping to develop processes with regards to environmental tuning, be regularly trained and assessed to support the day to day running of the SOC.
3. Tools/systems – The SOC tool set should be far more than just a SIEM platform (although this is a key element). The addition of host based agents, network captures, TI products, honeypots, etc is as important.
How effective and intelligent your SOC toolset is and how efficiently it is used will directly impact its utilisation. The SOC platform should not be considered a single or standalone SIEM product that will protect your entire organisational security. The initiative should be taken to see what other tools can be used in conjunction to generate more intelligent alarms and events for example, IDS/IPS as well as other state of the art cyber intelligence tools to work cohesively with the SIEM solution.
4. Processes - So what happens when you detect a threat? Is there panic and mayhem or is there a set process in place with an efficient escalation process specifically for that process? If they exist, how regularly are these processes reviewed? Processes in this context are a means of regulating different scenarios and the need to be reviewed, created, deleted or amended as required to ensure maximum efficiency. They do not apply just to alarm escalation but also day to day tasks which will allow regulate duties among team members.
So, what about 24x7?
So before you insist on 24x7 being the key factor in a SOC service, bear in mind that there may be some significant hurdles to cross to achieve this, and that the rewards vs the costs may not be the right decision for you. Staffing a 24x7 SOC is significant. Evenings, weekends and holidays all need to be covered. Finding enough work for the team throughout the night can be a challenge and remote working can be very demoralising. Managing staff handovers, conducting training and knowledge sharing between shifts all can be problematic.
Many SOC’s will operate their IR and deep dive capabilities during the day and on a call out basis.
The far more important first questions to ask are the ones outlined above. Ultimately, if these can be achieved then your assurance levels will be much greater. 24x7 on its own is no guarantee that you will have a high level of assurance.
If a SOC is working to optimal standards in the areas as outlined above, then there may be little need to have an eyes on screen service 24x7, as genuine threats would be correctly detected, classified and acted upon.
To contact Nettitude’s editor, please email media@nettitude.com