Much has been said in the last few years about the potential for blockchain-based technology to radically change the way in which financial and commercial transactions are executed. The way that it would achieve this is by disintermediation: removing the need for a trusted intermediary to facilitate each transaction, and allowing business to be conducted in a peer-to-peer manner.
How is this disintermediation made possible? In its most basic form, a blockchain is a type of distributed database which (ideally) has the following characteristics:
- Once records have been committed, they cannot be modified, deleted or reordered.
- All users of the database see the same set of committed records in the same order.
- There is no single point of failure which could affect the integrity or availability of the database.
Depending on the application there would typically be additional functionality built on top of the basic capabilities of the blockchain. For example, a blockchain intended for recording cryptocurrency transactions would only allow records meeting pre-agreed validity criteria, such as not spending the same money twice or money that you do not have.
The database records – or ‘blocks’ – are organised as a chain, hence the name ‘blockchain’. Each block contains a ‘hash’ of the previous block, calculated using a cryptographically-secure hashing algorithm. This is designed to be highly sensitive to changes in the block content, and easy to calculate in the forward direction but very difficult to reverse. The BitCoin blockchain uses a well-known and well-understood hash function called SHA256:
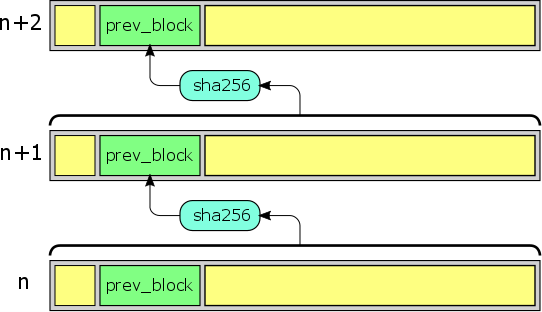
The hash allows the content of the preceding block to be validated, so once you have confidence in the provenance of one block you can then follow the chain to validate all previous blocks.
Conventional ACID-compliant database management systems can very easily meet the first two of the requirements listed above, and in sometimes have high-availability capabilities which go half-way towards meeting the third. What they do not provide for is distribution of trust. Consequently, where there is a need for two or more mutually-distrusting parties to have shared access to such a database, it would usually be necessary to appoint a neutral third party to administer it.
Blockchains do away with trust in any single entity by replacing it with:
- Trust in cryptographic algorithms, for those aspects of the problem that can be solved technically, and
- Trust in the majority of blockchain participants behaving honestly (or at least, not in collusion with each other).
These two forms of trust are brought together in a concept called the ‘proof of work’. In order for a new block to be added to the chain, it is necessary to solve a mathematical problem requiring a substantial amount of computational effort. Ideally there will be many participants all trying to do this independently, and it is typically the first to succeed who has the privilege of choosing which block is added.
In the case of the BitCoin blockchain, the puzzle is based on the same message digest function that is used to ensure integrity of the chain. Each block contains a ‘nonce’, a sequence of bits with no meaning which can be chosen freely by the creator of the block. The puzzle is to choose the nonce such that the double SHA256 hash of the block falls within a particular range. The size of this range determines the difficulty of the puzzle, which is adjusted approximately once per fortnight in order to maintain a success rate of approximately one block every 10 minutes. If there is no solution then a small change is made to the block content and the process repeated.
For example, consider block #479511 of the BitCoin blockchain. At the time this block was created, the difficulty target (in hexadecimal) was:
0000000000000000014735000000000000000000000000000000000000000000
It would therefore have been necessary to find a nonce which results in a block hash lower than this target. In this instance a solution was found when the nonce is set to c346450a. To illustrate this, it is possible to reproduce the final few steps of the search:
block + c3464506: 57ac5fcdbc616d4d487fca84e2fd59d675694c3685984e0592a6369143a679f2
block + c3464507: bd2c98d93ec322ce07837c0e61ba13e5b46a6b464eb334719a291efa573ca012
block + c3464508: 95e0d8bbeadf91a1f93fe380a641d3c0b38efe33d448c0deee6a57cf1d872255
block + c3464509: b33f540ea52ac6c4759cce8e4b5e9adf555695a1d8682d3764ddfd5ffe227fac
block + c346450a: 00000000000000000055f1a6a81e007e9825aa025b08f4c2353eb833ad724e3c
The prospect of successfully solving the proof of work for any given blockchain participant depends on a combination of the computational resources at their disposal, together with a large element of luck in terms of choosing the right content for the block. Consequently, provided that the available computing resources are reasonably well-distributed, no single participant can dominate the creation of new blocks. This allows all participants to play a part in ensuring the integrity of the blockchain, by choosing which previous block they are willing to build upon.
For example, consider the following two ways in which a dishonest participant might try to subvert the blockchain:
- A block could be added which does not meet the defined validity criteria. Other participants will decline to extend the chain in this direction, and instead base their efforts on an earlier, valid block. Their branch of the blockchain will quickly outgrow anything that can be created by the dishonest participant.
- Instead of building upon the most recently-added block, a fork in the chain could be created by building upon a different block. If this were successful it would have the effect of wiping out part of the history recorded by the blockchain. There is some risk here in relation to the most recently-created blocks, which is why care must be taken as to when blocks are considered to be irrevocably committed. Older blocks are protected because, in the event of a fork, participants favour the longest chain offered – and it is not possible to quickly create a long chain because of the proof of work requirement.
Both of these protections rely upon have a competitive and diverse community of participants. This is not a concern for major cryptocurrencies such as BitCoin and Ethereum, since there are sufficient economic incentives (transaction fees and creation of new currency) to justify large computational resources being dedicated to mining. For smaller-scale blockchains, however, they cannot be taken for granted. The effort spent mining must be proportional to the assets at risk in order to provide adequate protection.
Cryptocurrencies were the use case for which blockchains were originally developed, however many other possible applications have been conceived of since. The circumstances where it is likely to be useful are where you have a community of users who are willing to cooperate according to an agreed set of rules, but need assurance that no individual or small group is able to cheat. Uses that are already being explored include identity management, domain name registration, insurance and notarisation.
