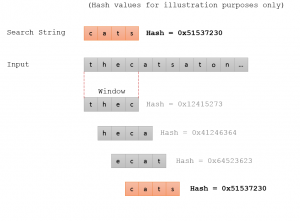
At Nettitude we collect a large amount of malware binary samples, both from our Honeypot network, from our customers and from incident response. One of the first steps we take is to calculate the MD5 hash of the malware and compare this hash to known samples, while unknown samples can be examined further by an analyst.
Tom Wilson
Recent Posts
Context Triggered Piecewise Hashing To Detect Malware Similarity
Posted by
Tom Wilson on Jun 30, 2015
0 Comments Click here to read/write comments
Topics: Security Blog, Uncategorized
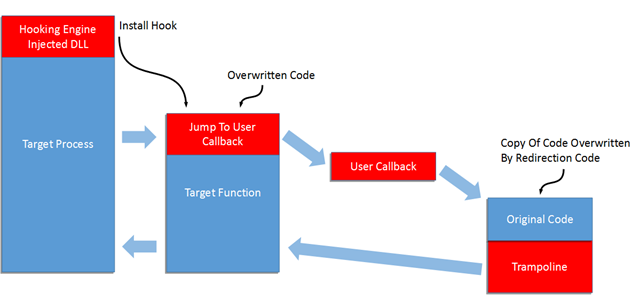
Hooking can be used by legitimate software for reverse engineering, for example, to examine the user mode function calls that a malicious program is making.
0 Comments Click here to read/write comments
Topics: Security Blog, Uncategorized
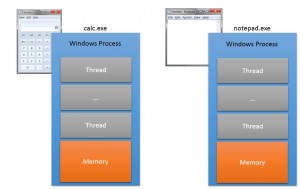
In a previous blog post I gave a high level overview of DLL injection, what it is used for and how it might be achieved.
0 Comments Click here to read/write comments
Topics: Security Blog, Uncategorized