Building Baseline Security in the Cloud with Policies
AWS (Amazon Web Services) policies
Microsoft Azure policies
How implementing baseline policies in a cloud environment helps
Cloud security can often feel like an overwhelming practice. Cloud environments can employ many resources with varied functions, leading to the complicated task of securing these resources. Implementing baseline policies within your cloud environment can simplify the task of implementing common security practices uniformly across all resources. Cloud providers simplify this practice through policy-checking services. In Amazon Web Services (AWS), the service is called Config, while in Azure the service is called Policy.
Within AWS Config and Azure Policy, there are policy deployments in line with the Center for Internet Security (CIS) recommendations. The CIS issues a document with configuration recommendations for common services within cloud deployments. These services include identity management, compute, storage, networking, monitoring, and database configurations. For AWS, the list of recommendations is approximately 60 items. Instead of examining each item within a document, using AWS Config or Azure Policy can automate the process and alert you to many misconfigurations within minutes. This offers quick and easy deployment of baseline security configurations and continuous monitoring of the compliance state of those policies within the environment.
The following sections detail how to implement these baseline policies for AWS and Azure. It should be noted that some costs may be incurred related to the use of these services.
AWS (Amazon Web Services) policies
What is AWS Config?
AWS offers Config as their policy checking service. AWS Config is a service that permits the monitoring of all environment resources and the deployment of configuration rules. Templated conformance packs exist which retain large groups of rules. These templated conformance packs are publicly available via the link below:
https://docs.aws.amazon.com/config/latest/developerguide/conformancepack-sample-templates.html
Nettitude recommends that, at a minimum, the ‘Operational Best Practices for CIS AWS Foundations Benchmark v1.4 Level 2’ conformance pack is deployed within your AWS infrastructure. You may also deploy custom rules within your environment to meet your unique organizational security policies.
To start with, Config should be enabled. The enabling of AWS Config is a click-through scheme detailed here:
https://docs.aws.amazon.com/config/latest/developerguide/gs-console.html
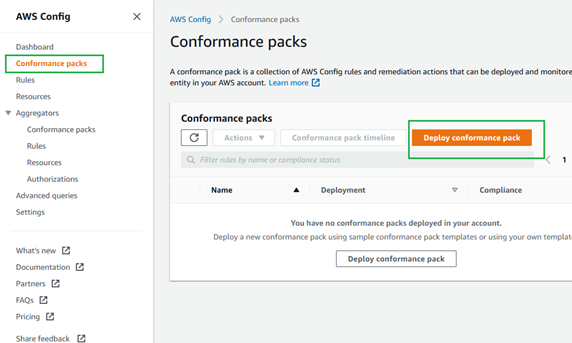
With Config enabled, navigate to 'Conformance packs' then click 'Deploy conformance pack.'
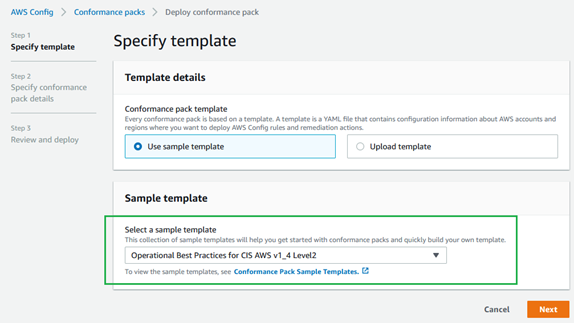
On the following page, select the sample template ‘Operational Best Practices for CIS AWS Foundations Benchmark v1.4 Level 2’.
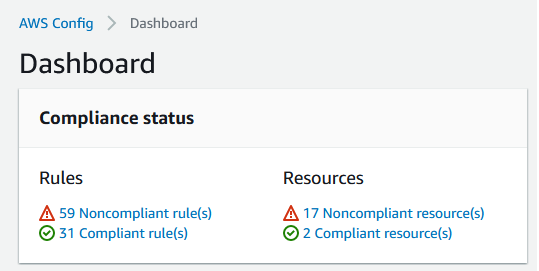
In the following pages, you will be asked to name the conformance pack and to deploy it. Once that conformance pack is deployed, the Config dashboard will show the compliance status of each rule within the conformance pack. The compliance of the environment will be shown on the Config dashboard.
By clicking on the name of the conformance pack, you can view each rule and the compliance status of that item.
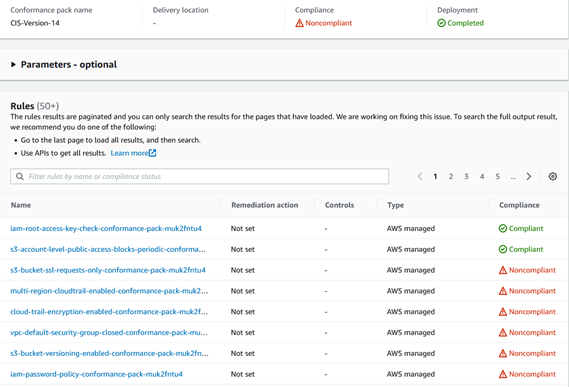
The automatic remediation actions within this conformance pack are not set, so in each instance, you will need to check the noncompliant rule and manually change the configuration for the affected resource. By clicking on the rule, you will be provided with the description and the affected resources.
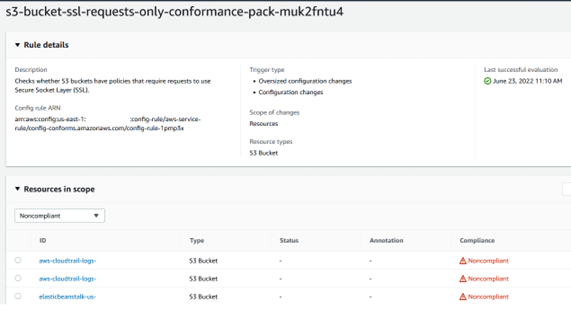
Once remediation action has occurred, you may rerun the rule to note the compliance update.
Microsoft Azure policies
What is an Azure Policy?
Microsoft Azure offers the Policy service. In a similar manner to AWS, this service permits the deployment of CIS rules within the environment and the monitoring of the associated rules. By default, Azure implements the ASC Default policy which retains many Microsoft recommended practices. The name of the built-in is ‘CIS Microsoft Azure Foundations Benchmark 1.3.0’ the rules are detailed here:
https://docs.microsoft.com/en-us/azure/governance/policy/samples/cis-azure-1-3-0
To implement this policy, navigate to Azure Policy, then the 'Assignments' tab, and click 'Assign initiative'. This function is also on the 'Compliance' tab.
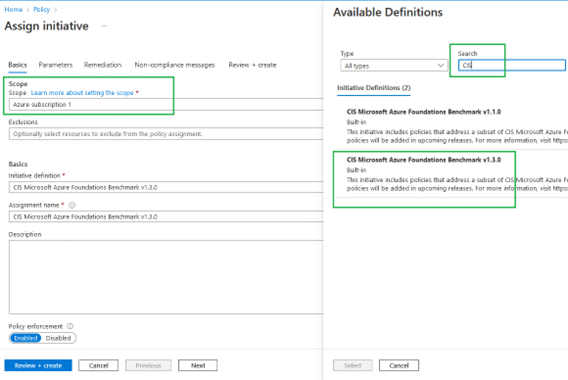
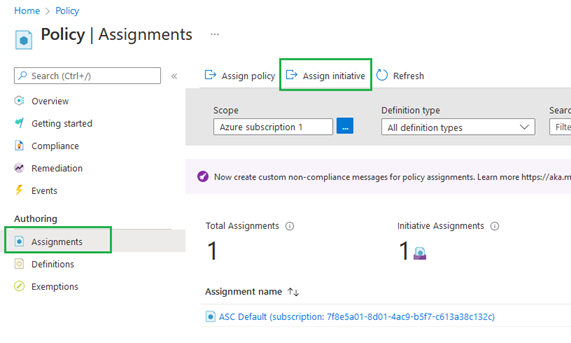 On this page, designate your subscription and within the 'Initiative definition' field search ‘CIS Microsoft Azure Foundations Benchmark 1.3.0’. Select that initiative definition and review and create the initiative.
On this page, designate your subscription and within the 'Initiative definition' field search ‘CIS Microsoft Azure Foundations Benchmark 1.3.0’. Select that initiative definition and review and create the initiative.
Once the initiative is deployed and run, you may view the compliance state of the rules on the overview page.
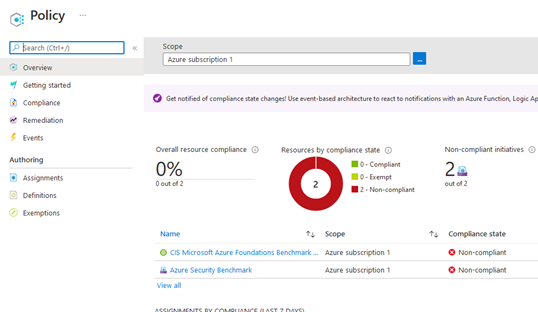
By clicking the name of the initiative, you can view the status of the particular rules.
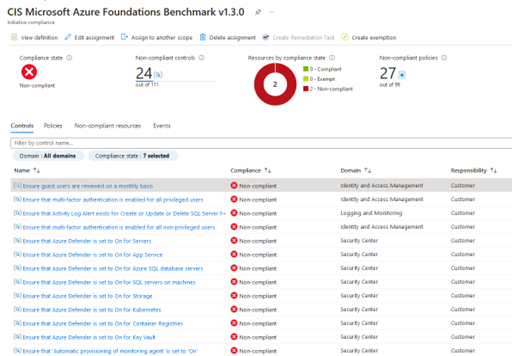
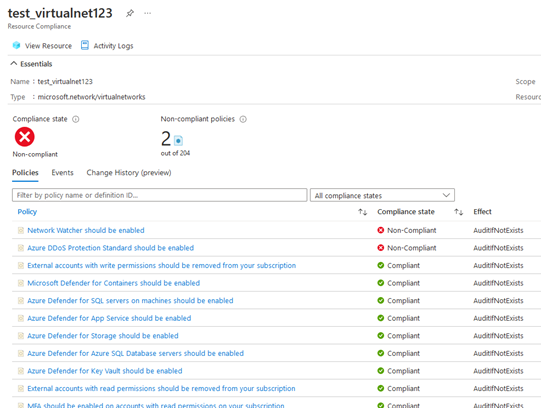
You may also note the compliance of resources within the environment.
How implementing baseline policies in a cloud environment helps
Implementing appropriate policies can quickly and easily help account holders with identifying and correcting misconfigurations. This effort can lead to a drastic improvement in security and allows monitoring improvements of assets as they are deployed within the cloud. The CIS benchmark checks are readily available for deployment in Azure and AWS to address common security misconfigurations. All cloud users should deploy policies within their environments to build baseline security.
Find out how Nettitude's team of AWS Security and Microsoft certified consultants can help you with Cloud Penetration Testing and Configuration Review services or contact solutions@nettitude.com.








