By Nettitude
Today, we’re excited to announce the launch of our Nettitude Bug Bounty programme .
Over the past few months, we’ve been running a Bug Bounty trial with a number of our clients, which we’re pleased to say has been successful. Now, we’re ready to open our Bug Bounty service up to the world.
Where does a Bug Bounty programme fit in?
As a leading cybersecurity service provider, we’re privileged to work with our clients on some of the most difficult security problems facing organisations today. Our technical assurance teams are experts in a number of fields, e.g.
-
- Vulnerability Assessment – whether it’s point in time or continuous assessment, our clients benefit from the assurance provided by automation. The focus here is on assessing protection measures. Breadth of coverage is easily achieved, but for depth, you need…
- Penetration Testing – human skill is used to uncover as many vulnerabilities as possible at a point in time. This provides a greater level of assurance, and augments vulnerability assessment well. If your organisation wants to understand protection, detection and response to real world threat actors, it’s likely that you’ll opt for…
- Red Teaming – scenario based testing against specific objectives using real threat actor tactics, techniques and procedures. It’s a depth first assessment, and focuses on detection and response, not just protection.
A Bug Bounty programme provides some of the features found across these three methods of assurance, as well as some unique features of its own. Consequently, organizations are increasingly augmenting their assurance programme with bug bounty services.
Some of the reasons for that include:
-
- Bug Bounty hunters are given the freedom to prioritise depth of testing in a manner that would not be conducive to a high-quality penetration test.
- A continuous and long-term testing time frame ensures newly introduced vulnerabilities are quickly identified.
- Access to a larger group of professionals, all of whom have complementary skill sets and experience.
- A cost of service based on vulnerabilities identified rather than time spent testing.
Penetration tests are an important part of an effective assurance programme. Bug Bounty programmes augment that and combined, they bring even greater levels of assurance.
The Nettitude bug bounty process and approach
Why choose Nettitude to provide a Bug Bounty service for your organisation?
Trust
First and foremost, comes peace of mind. We’ve spoken to CISOs the world over about their experiences with Bug Bounty programmes. By and large, their feedback has been that such programmes provide real value. Then, there’s usually a pause, followed by a “but”. That “but” tends to be concern around the trustworthiness of the people conducting the testing.
It’s not uncommon to hear about Bug Bounty hunters straying well out of scope, sometimes intentionally. For a critical production system, that presents an unacceptable risk. Where CISOs have mandated background checks, the quality of findings usually then falls. Unsurprisingly, some of the most talented people are not open to background checks.
Our team are background checked, security cleared, known and vetted entities. They also happen to be some of the most skilled security professionals in the world.
Safety
Bug Bounty programmes usually include a lot of production infrastructure in scope for testing. With this, are inherent safety requirements. Trust and safety represent two of our very highest priorities.
Our fully background checked bug hunters all test from the same IP address range, so you can easily attribute any testing activity to Nettitude. Our team draws upon many years of experience to conduct their work safely and methodically; your programme will be run under the same risk management controls that we’ve continuously developed since 2003.
Coverage
Bug Bounty programmes typically focus on internet facing systems as a matter of practicality. We can leverage our remote testing technology to safely test internal systems and other less traditional Bug Bounty scope.
Effective Bug Bounty Process
Our bug hunters are the same talented and experienced people that make up out Penetration Testing Team, our Red Team, and our Research and Innovation Team. They’re the same people who have spent years assessing the production systems of central banks, critical national infrastructure, government, and plenty more. Together, they’ve compromised some of the most well secured systems on the planet. Today, we’re bringing that collective talent to our bug bounty service. We will find vulnerabilities that others can’t, and you’ll be shielded from low quality findings.
Value
Your programme will be managed by one of our offensive security professionals. They each have a long history of penetration testing expertise and are dedicated to ensuring the smooth operation of your Bug Bounty programme, from start to end. The programme manager will work with you from the very beginning to ensure that the programme design meets your objectives in the most effective manner possible. They will review all submissions for quality before they’re released to you. They will be your primary point of contact for all things Bug Bounty related.
When we find previously undiscovered vulnerabilities in third party software, otherwise known as 0days, we will be happy to leverage our coordinated disclosure team to quickly and effectively work with the vendor to get their product patched and your environment secured.
Of course, we’ll retest any given vulnerability over and over until both your organisation and our bug hunters are confident that it’s been successfully remediated. You’ll get direct access to our team of security professionals via our online portal.
Oh, and did we mention? All of this is free of charge! No management fee, no disclosure fee; pay for vulnerabilities and only vulnerabilities.
Our Bug Bounty Platform
We run our Bug Bounty service via an online portal. This ensures a consistent and repeatable service that you can access on demand.
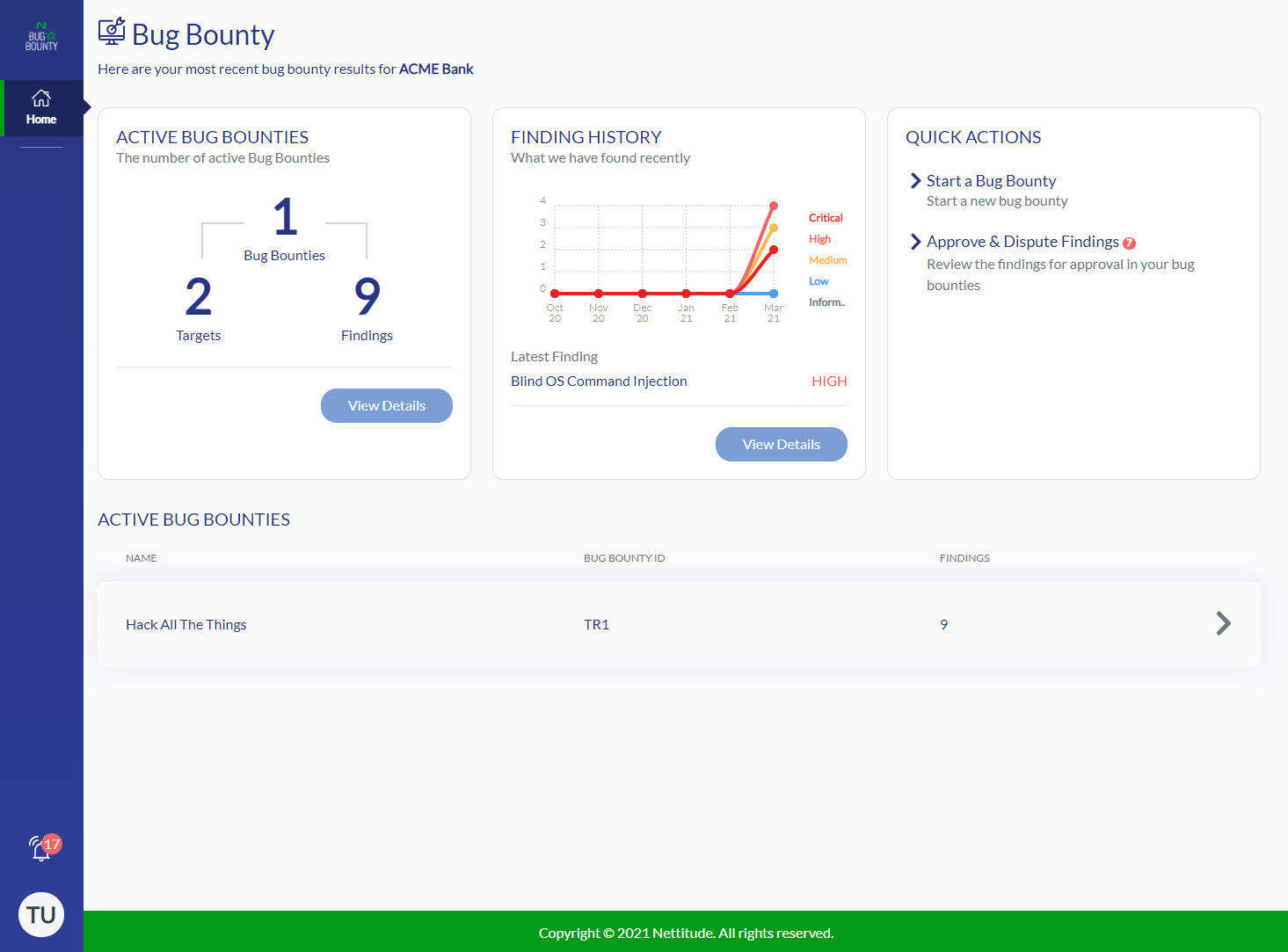
Just a few of our platform features include:
- A full featured web application allows use from any platform, anywhere.
- An easy to use API. Integrate your systems with our platform for maximum flexibility, or use one of our point and click integrations for common platforms such as Jira.
- Role based access controls. Allocate different levels of access to your employees.
- Customisable notification controls. Prefer to be notified of a critical vulnerability by SMS while a medium vulnerability can be by email? It’s up to you.
- Detailed vulnerability reporting; see impact, reproduction, evidence, remediation, and more.
- Access to our team through the inline comment system.
- A robust vulnerability acceptance process.
Of course, there’s plenty more besides.
Sign Up
We would love the opportunity to talk to you more about our Bug Bounty service. To find out more, please contact your local team.
Learn more about our incident response services.







