By LRQA Nettitude
‘Houston, we have a problem…’
The operational resiliency of the financial services sector is of paramount concern to governments and regulators across the globe. A catalogue of high-profile breaches suggests that board level engagement and awareness of how to prepare and respond to a cyber event is frequently misunderstood or inadequate. Although these boards believe that they are taking steps to combat the cyber threat, their strategies are frequently poorly grounded and misaligned.
To address this, a number of regulator-driven frameworks for assessing financial institutions cyber preparedness, protection, detection and response capabilities has matured, and proliferated across multiple regions around the globe. In this five-part blog series, we’ll outline the main regulatory frameworks for the UK, Europe, Singapore and Hong Kong. In the first post, we’ll take a look at the UK’s regulatory framework – CBEST.
The UK Approach – CBEST
In 2014, a more proactive stance was taken by the BoE and the Financial Conduct Authority (FCA), who asked CREST to develop a standard that could be used to test operational cyber resiliency within the systemically important financial infrastructure of the UK’s financial system.
This brought into existence the STAR (Simulated Targeted Attack and Response) framework that then became the basis on which CBEST was built. The CBEST framework aimed to deliver regulator driven bespoke intelligence-led cybersecurity testing within the UK financial sector against live operational systems. The need to understand the real-world risks was essential and therefore a robust risk management process was built into CBEST from the outset.
CBEST Objectives
The CBEST framework set out to achieve the objective of increasing the UK Financial Sector’s resilience to cyber-attack, but also support the following:
- Access to advanced and detailed cyber threat intelligence;
- CBEST Testing of live systems;
- Access to knowledgeable, skilled and competent cyber threat intelligence analysts, who have a detailed understanding of the financial services sector;
- Realistic penetration tests that replicate sophisticated, current attacks based on current and targeted cyber threat intelligence;
- Access to highly qualified penetration testers that understand how to conduct technically difficult testing activities, whilst ensuring that no damage or risk is caused;
- Confidence in the methodologies utilised by the companies within CBEST for conducting these sophisticated and sensitive tests;
- Confidence that the results and the information accessed by the testers will be protected;
- Standard key performance indicators that can be used to assess the maturity of the organisation’s ability to detect and respond to cyber-attacks;
- Access to benchmark information, through the key performance indicators, that can be utilised to assess other parts of the financial services industry including the Bank of England; and
- A framework that is underpinned by comprehensive, enforceable and meaningful codes of conduct administered by a specialist professional body.
The 3 Phases of CBEST Testing
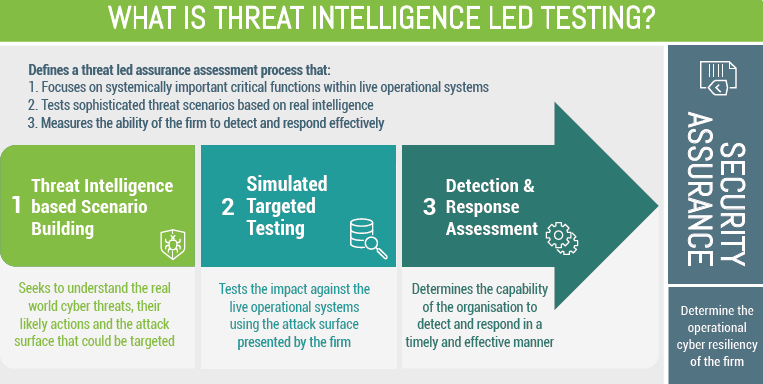
CBEST is regulatory led where the scope of the Critical Functions (CFs) and Business Critical Functions (BCFs) to be included are agreed at the outset. A CBEST consists of three phases as follows:
- Threat intelligence is conducted to identify and understand not only the most likely and most significant threat actor’s capabilities, but also the threat surface as presented by the firm/FMI under test. A set of credible scenarios is created and supported by a targeting pack of information about the people, processes and technology that fall within the scoped threat surface. This work is conducted by an accredited external supplier and reviewed by the regulator and the UK Government’s National Cyber Security Centre (NCSC).
- An intelligence led penetration test is then conducted for each of the selected scenarios where the TTPs deployed by the identified threat actors are enacted on the live operational systems. Testing on live operational systems was a key aspect of this approach set out by the BoE to ensure that all findings were based on reality.
- A Detection and Response Assessment (DRA) is then conducted to assess the firm’s/FMI’s ability to detect and respond to the actions conducted during the test. A set of KPIs are measured around the firm’s ability to conduct their own threat intelligence and the state of their detection and response.
What are the Results of a CBEST Assessment by LRQA Nettitude?
CBEST is not a pass or fail exercise, but it produces a series of learnings and recommendations, which are to be presented back to boards and senior executives as well as the regulators. Post-test follow-ups are then managed through normal regulatory interactions/channels.
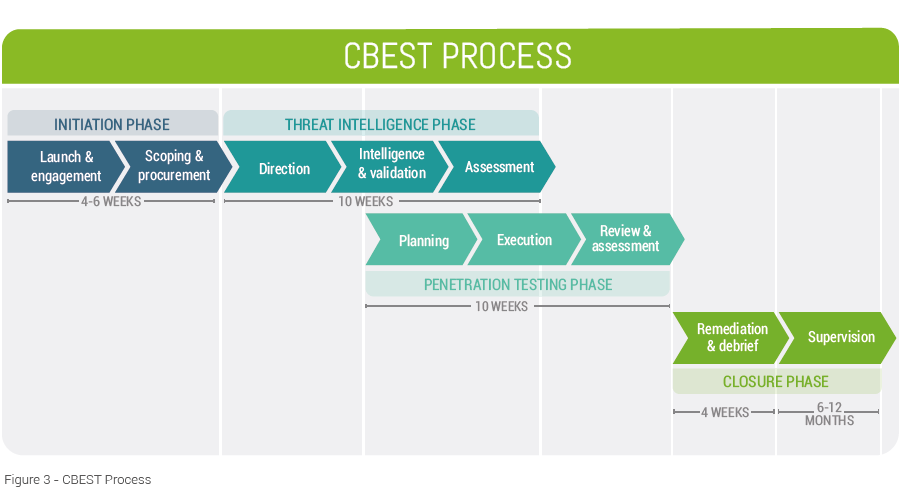
The below diagram outlines the CBEST process –
What is the Time Scale of a CBEST Assessment?
The CBEST framework highlights that the phases only represent a logical review of the tasks and there will be significant overlap. There is scope for activities to start earlier and run in parallel with others in order to increase efficiency, given the limited timescales of the assessment. The overall engagement time-frame between launch and supervision can vary considerably but is outlined as approximately twenty-two to thirty weeks.
Figure 3 presents a more realistic depiction of a physical project plan to complement the logical phases.
How Should You Respond to CBEST Requirements?
Cyber-risks have been traditionally hard for executives and organisations to understand due to the highly technical nature of the events and the obscure language used to describe and explain them.
Organisations that have been through threat led simulations and have experienced first-hand the likely impacts of a cyber-attack are characterised by a step change in understanding, appreciation and realisation of the potential impacts.
Nettitude would encourage all organisations, financial or other, to support and embrace a threat led assurance process, as depicted in the emerging regulated standards.
Need more advice, contact our expert team with how we could help you prepare to meet CBEST requirements, or find out more about our CBEST Penetration Testing services.