By Joel Snape | Security Researcher at Nettitude

One of the key enablers of business modernisation and efficiency in the Maritime Industry has been the availability and adoption of VSAT satellite connectivity. This has allowed vessels to stay connected to shore-based networks throughout their voyage: providing internet and corporate network access for crews and passengers; increasing the amount of administration which can be carried out at sea to save time in port and enabling remote monitoring and management of on-board systems.
Satellite networks are often treated as ’extensions’ of corporate networks and are therefore used to transfer important internal information relating to business operations and crew. There has long been an assumption that listening in to ‘satellite signals’ is difficult because of the high-frequencies used and subsequent cost of reception equipment. This assumption, coupled with the long operating life of costly satellite equipment, has led to a system in widespread use which is much easier to abuse than when first deployed.
This blog post will look at the pitfalls in VSAT technology, it's history of hacking, and the learning points we can take away from the secrets of the Maritime Communications mishaps. We will then lead on to some valuable conclusions for moving forwards, in the hope of further developing the cybersecurity of Maritime communications.
What has been discovered?
New capabilities to intercept VSAT communications and potentially inject traffic using consumer-grade hardware have been demonstrated by researchers from Oxford University and the Swiss Federal Office for Defense Procurement (Armasuisse) in their paper ‘A Tale of Sea and Sky: On the Security of Maritime VSAT Communications’ published in the 2020 IEEE Symposium on Security and Privacy. Their research allowed them to observe internal emails, file transfers and documents containing sensitive business and personal information. This highlights the need to treat VSAT networks as ‘public’ in the threat-modelling you carry out, and ensure other mechanisms are in place to protect the confidentiality, integrity and authenticity of the information they carry.
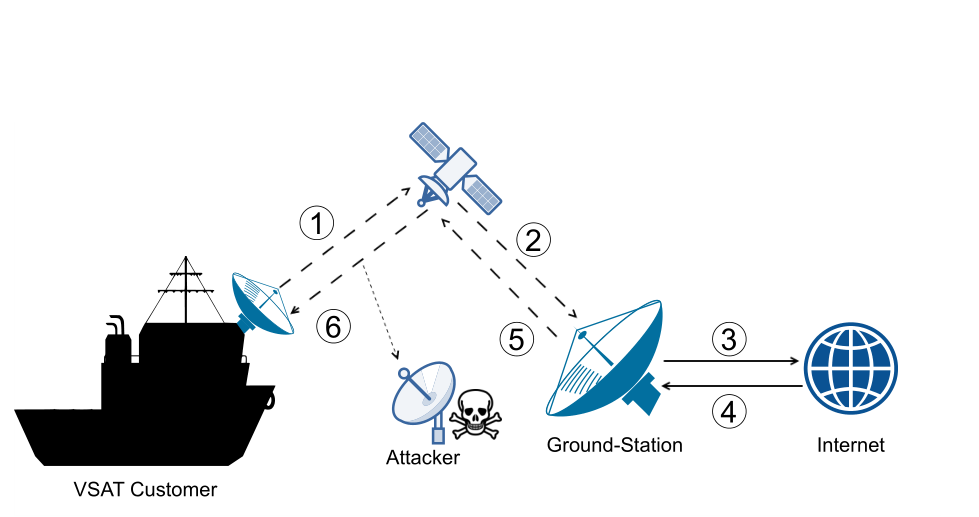
The research team were able to intercept the ‘return leg’ of communications between vessels and land-based systems. (Source: "A Tale of Sea and Sky: On the Security of Maritime VSAT Communications")
What is the history of VSAT hacking?
It’s long been known that network traffic sent over satellite links is sent in plaintext and can be intercepted, in which there is evidence as far back as 2015 that nation-state groups such as Turla have (ab)used this to retrieve information from organisations they have attacked. However, previous research and demonstrations such as this from S21 at CCC 2010 have been limited to older transmission standards (DVB-S) and the high-frequencies used have meant many operators have deemed this too difficult to be a risk.
Satellite internet access typically works by using a geostationary satellite to receive signals from ships and relay them to ground-stations where they are then forwarded on to the internet. Return messages are then sent to the satellite, where they are broadcast back to the ship. However, the satellite is aiming to serve clients over a wide geographical area and so the return messages can be received by anyone in the satellite’s coverage area.
What was different about this Maritime VSAT research?
In this new demonstration, the research team were able to use standard satellite-TV hardware available for approximately $400 to receive communications using the newer DVB-S2 GSE standards, and decode it to obtain the raw network traffic being returned from the satellites to the vessels. Using a week’s worth of recorded traffic from four service providers they were able to extract traffic from over 9000 distinct hosts using the satellite network, and in a random sample of IP addresses identify the specific owners or fleets about 25% of the time.
The researcher’s ability to recover useful information from the traffic they intercepted was limited by the hardware used, but they were still able to recover between 60% and 85% of bytes transmitted - enough to start extracting application data.
Despite only having data for a relatively short time-period, the research team were able to observe sensitive information from both standard IT applications (e.g. email and web) and Maritime specific OT products and protocols such as ECDIS, AIS navigation and fleet-management solutions.
From the standard IT messages seen, the researchers were able to obtain sensitive information such as names and personal information about crew-members, password hashes for intranet accounts and internal business discussions relating to a recent accident and death of a crew-member. Additionally, OT communications included information on how to automatically deliver ECDIS updates, cargo manifests and potentially sensitive passenger credit-card information from payment terminals on a cruise ship.
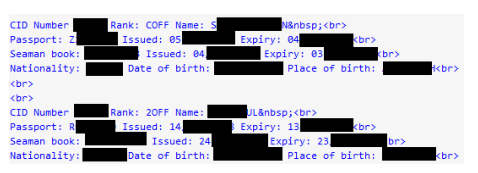 Crew passport information obtained by the researchers (Source: "A Tale of Sea and Sky: On the Security of Maritime VSAT Communications”)
Crew passport information obtained by the researchers (Source: "A Tale of Sea and Sky: On the Security of Maritime VSAT Communications”)
The team also successfully demonstrated a ‘man-on-the-side’ attack where a connection initiated from a terrestrial host to a service on a vessel can be ‘hijacked’ by an attacker with the ability to observe VSAT traffic. This could be most simply exploited to cause a denial of service for all or some connections to the vessel, or in a more advanced attack inject content or spoof responses (e.g. false status information).
What do we take away from this?
The skills and knowledge to be able to carry out this attack remain relatively specialised, but it is worth noting that the recent launch in 2018 of the Es’hail-2 geostationary satellite containing two amateur-radio transponders has led to a surge in public interest in receiving satellite communications. Although the frequencies differ, it has proved a good introduction into receiving high-frequency satellite signals and there have been a large number of tutorials and articles published. These cover how to construct the necessary antennas and processing equipment to be able to receive and demodulate its DVB-S2 signals using relatively cheap commodity equipment, which means that it is no longer possible to rely on the cost and complexity of radio equipment capable of processing satellite frequencies to obscure VSAT communications.
What do you need to think about if you are a VSAT user?
VSAT network connections have often been sold as and modelled as extensions of corporate intranets and so the adoption of encryption has been slow when compared to applications and services accessed over the internet. This research shows that the threat-modelling used for Maritime networks needs to be updated to mitigate the risk of messages being intercepted and potential traffic injection.
Defence against passive observation is possible through the adoption of encrypted protocols such as HTTPS or IMAPS which provide assurance of confidentiality and integrity when properly implemented. Defence against potential traffic injection is a more challenging technical problem as traditional VPN solutions often add too much overhead to a satellite connection or are incompatible with proxies used to improve the performance of the satellite link.
For more information on creating securer communications within the Maritime sector, please download our free whitepaper. In addition, don't hesitate to contact your local Nettitude team.
Images sourced from J. Pavur, D. Moser, M. Stohmeier, V. Lenders and I. Martinovic, "A Tale of Sea and Sky: On the Security of Maritime VSAT Communications," in 2020 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, US, 2020 pp. 1025-1041.







