By Chris Oakley | VP of Technical Services for the Americas at LRQA Nettitude
The importance of detection and response
It is common for organizations seeking to improve their security posture to focus on prevention-based practices. This approach aims to stop threat actors from breaching the organization’s infrastructure, which is an important component of a robust security posture and should continue to be a focus.
In the following post, we'll take a look at the objective of effective security and how the SOC Visibility Triad plays an important part in this.
The objective of perfect security is noble but, pragmatically, unachievable. As Professor Gene Spafford famously once said:
“The only truly secure system is one that is powered off, cast in a block of concrete and sealed in a lead-lined room with armed guards - and even then I have my doubts.”
Gene Spafford; “Computer Recreations: Of Worms, Viruses and Core War", by A. K. Dewdney in Scientific American, March 1989, pp 110.
If perfect security is unachievable, then we must entertain the possibility – perhaps even the likelihood – that a given system will be compromised during its lifetime. With the assumption that a compromise is likely to occur regardless of preventative security posture, we can start to establish a strategy to limit the impact of that compromise. This leads us to detection and response.
Increasingly, organizations are broadening their objectives to include detecting malicious activity in real-time and responding to it quickly and effectively.
Security Operations Center
For infrastructure of even modest size and complexity, it quickly becomes apparent that a dedicated function is required to handle detection and response effectively.
If a genuine capability is desired, it is not enough for one or two members of an IT team to have this as an added responsibility, trying to live off the land with whatever tools and training they already have. Rather, it is necessary to establish a Security Operations Center (SOC) that has a strong focus on continuously developing its people, process, and technology.
One of the early problems a SOC will quickly need to solve is the ability to have complete visibility into each part of the infrastructure they are tasked with monitoring.
The Challenges for a new SOC
A new SOC faces several challenges. There are all sorts of tools and technology available, all claiming to do to similar-but-different things and competing for the SOCs presumably finite budget. So, where to start?
Commonly, the SOC capability begins by focusing on ingesting logs from various sources. A Security Information and Event Management (SIEM) product is implemented. Things look good and the team is optimistic.
Fast forward a few weeks. SOC analysts are overwhelmed with logs providing questionable value and alarms that are not tuned to the environment they are protecting. Worse, the sea of false positives allows genuine alerts to be missed, the logs do not provide full visibility into the network, and morale amongst the team starts to fall. This is not a strong foundation on which to build an effective detection and response capability.
The SOC Visibility Triad
The SOC Visibility Triad, described by Gartner in 2019, moves beyond SIEM-as-a-SOC and towards a more network-centric approach. The triad consists of three pillars -
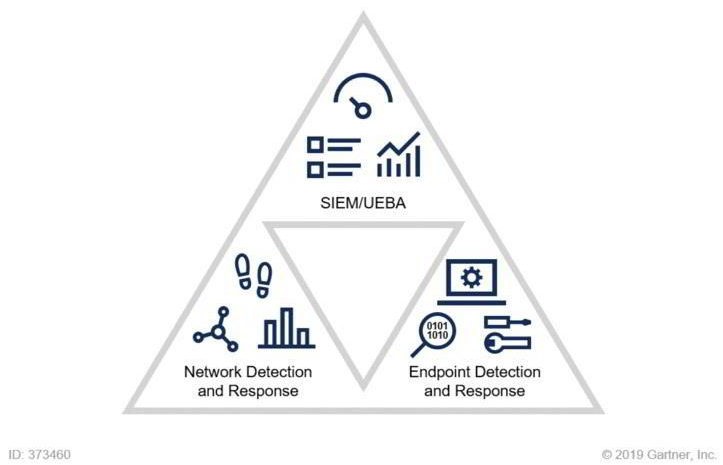
Pillar 1 - Security Information and Event Management (SIEM)
Security Information and Event Management (SIEM) gives log collection and aggregation capability to a SOC. Such logs can come from almost anywhere, e.g. endpoints, custom applications, cloud services, other security tools, etc. Analysts can then analyze these logs effectively, in aggregate, and in a common format. Efficiency gains lead to an improved capability and earlier detection. A SIEM is an important part of any SOCs infrastructure.
Increasingly, User and Entity Behavior Analytics (UEBA) technology is also being adopted by defense teams to complement SIEM. Where traditional SIEM solutions rely heavily on preconfigured correlation rules and attack patterns to identify suspicious events, UEBA goes further; it baselines user and other entity behavior to learn what “normal” looks like. Subsequent deviations from that baseline behavior can be identified and analyzed for security implications. This is especially useful for detecting attacks that are harder to identify – for example, zero-day exploits, insider threats, etc.
Pillar 2 - Endpoint Detection and Response (EDR)
The basic premise of Endpoint Detection and Response (EDR) technology is that it can detect malicious activity that occurs directly on an endpoint such as a laptop or server. Analysts can also use EDR during early-stage incident response to limit the impact of a given threat once it has been detected.
While antivirus technology typically relies on predefined signatures that can easily be evaded by targeted attackers, EDR is more behavior-oriented. For example, if a user opens a Microsoft Word document that in turn launches a PowerShell process, that sequence of events may be detected as suspicious enough for the action to be blocked and reported. EDR augments SIEM; an attacker may be able to delete logs before they can be used for detection, while their on-host activities may be flagged by EDR.
The response portion of EDR allows a network defender to quickly act once malicious activity has been confirmed. For example, EDR allows an analyst to remotely isolate the host from the network in such a way that only the analyst has access to that machine, for further remote investigation. In the meantime, the compromise is contained, and the attacker can no longer laterally move to other machines in the network.
Pillar 3 - Network Detection and Response (NDR)
Network Detection and Response (NDR) technology continuously monitors network communications to identify potential attacks that might not be as obvious from analyzing log data or on host activity. Real-time network data is generally immutable and is consequently considered one of the more objective sources of truth during analysis. If an attacker has evaded log and host-based detection, then network traffic analysis can reveal their existence.
Imagine a compromised employee laptop that has gone unnoticed. Perhaps preventative measures failed, a stealthy form of compromise was used, logs were deleted or modified, and on host detection methods have been quietly disabled. The laptop now has Command and Control (commonly known as C2) tooling on it and is being remotely controlled by an attacker. That control must, by definition, involve network communications. NDR technology may pick up on those C2 communications where on host and log-based detection methods have failed.
The challenge with NDR is that network traffic for even a small IT estate is high volume. The SOC will need to deploy such technology strategically, to avoid becoming overwhelmed, and to minimize the chance of an attacker being able to hide in the noise. When deployed thoughtfully, NDR provides a big boost to SOC capability.
Three is Better than One
As facets of the SOC visibility triad, SIEM, EDR and NDR all have areas of strength and weakness. The point of the SOC Visibility Triad is that each component augments the others; both false positives and false negatives can be minimized.
In a somewhat defeatist attitude, network defenders sometimes lament that an attacker only has to find one way into a network, whereas a defender must secure all areas robustly. We tend to disagree with that sentiment and flip it on its head; the attacker is playing on your home turf, and you can set many tripwires. Each action an attacker takes is an opportunity for detection and an attacker acting on objectives typically requires several actions. Making an attacker work harder to achieve undetected compromise adds friction to their operation. Friction adds to the cost for the attacker’s operations and increases the likelihood of detection.
Focusing on the three elements of the SOC Visibility Triad helps your defensive operation to focus on technology strategy, meet budget, and ensure that the technology is working for you not against you – allowing more time and budget to be spent on developing people and process, which is of high importance for effective operations.
LRQA Nettitude SOC Solutions
LRQA Nettitude have been running a 24/7 SOC for many years. Our highly capable solution defends client networks of all sizes and across a wide array of industries.
Although the SOC Visibility Triad was published in 2019, we have been using that model for a lot longer than that. Throughout that time, we have learned what works and what does not, and we continue to innovate and evolve our SOC capability. Our experts are continuously refining our detection and response capabilities, with real-time input from our team of threat intelligence analysts. Our world-class Red Team eats, breathes and sleeps sophisticated attack chains. When they are not breaking into central banks, critical national infrastructure, and government agencies (with permission, of course!) they work closely with the LRQA Nettitude SOC to test it and push our defensive capabilities to the next level. This constant cycle of expert attackers working with expert defenders’ results in our exceptionally effective SOC capability, which protects client networks around the world.
In a world of increasing attacker activity, industry regulation, laws, and fines, it is becoming more important to prioritize a strong detection and response capability, to limit the impact of inevitable attacks, and gain acceptable levels of security assurance.
Contact us to enquire about our SOC services.







