By Joel Snape | Cybersecurity Researcher at Nettitude
The NIST framework is voluntary guidance, based on existing standards, guidelines, and practices for organizations to better manage and reduce cybersecurity risk, produced by the National Institute of Standards and Technology. In addition to helping organizations manage and reduce risks, it was designed to foster risk and cybersecurity management communications amongst both internal and external organizational stakeholders.
Nettitude often base our guidance and solutions around this framework, in which there are some key considerations to be made when adopting cloud technology, based on the NIST framework. Continue reading to discover why the NIST Cybersecurity framework is used and how it relates to cloud adoption.
Read More
Topics:
Cyber Security,
Nettitude,
News,
Security Blog,
Cyber Security Blog,
Download Area,
cloud series
By Phil Buck | Senior Threat Intelligence Analyst at Nettitude
On a 24-hour basis, the Nettitude Security Operations Centre are monitoring our client’s digital environments for potential and current acting threats, in which our trained analyst experts are ready to detect and respond to alerts within a client environment. Through a threat- intelligence led approach, our teams use a number of tools and techniques, from deploying honeytraps, to reverse engineering malware, and monitoring our threat intelligence feeds, these activities are all in the typical day of our SOC team members. However, you may be surprised to hear that we also use social media as a tool to gather intelligence on potential threat actors.
Now that your ears have pricked up, continue reading our latest blog post to find out how social media is used as a viable source of threat intelligence!
Read More
Topics:
Cyber Security,
Nettitude,
News,
Security Blog,
Cyber Security Blog,
Download Area
By Nettitude Research and Innovation Team
Communication technologies and protocols are an essential part of a vessels electronic systems. However, the unique aspects of marine and offshore environments present challenges to their use; in which the nature of their use and the widespread use of legacy systems affect all security activities and agendas.
This has become a particularly high topic on the cybersecurity agenda over the last two decades, as the explosive growth in communications services has dramatically changed the way that businesses operate in all sectors, improving efficiency and providing new opportunities. In the maritime sector, we can see this from the original adoption of VHF a hundred years ago for ship communication, through to more recent safety technologies such as AIS and satellite communication. However, the limited bandwidth and high cost of these technologies has historically limited the sector’s ability to leverage them in many of the ways seen in other industries.
The following blog post will outline some of the key trends in cybersecurity vulnerabilities in technologies utilised by the Marine and Offshore sector.
Read More
Topics:
Cyber Security,
Nettitude,
News,
Security Blog,
Cyber Security Blog,
Download Area,
Marine and Offshore
By Joel Snape | Cybersecurity Researcher at Nettitude
In our previous blog post for the ‘Cybersecurity and the Cloud’ series, we looked at what considerations should be made when considering migrating to the cloud. To follow on, the next step is to establish a strategy for how you are going to migrate your business over to a cloud platform.
There are a number of options to choose from when considering what cloud platform provider you are going to go with. From public cloud spaces to private, community and hybrid; each one has its own benefits and drawbacks and establishing which one is best for your company will depend on the way you will be using it and what for. In order to ensure you select the right platform for your businesses needs, it is essential to establish a clear cloud migration strategy.
In this post, we’ll discuss the five key steps to take in order to create an effective cloud migration strategy.
Read More
Topics:
Cyber Security,
Nettitude,
News,
Security Blog,
Cyber Security Blog,
Download Area,
cloud series
By Graham Sharples | Threat Analyst
Internet of things (IoT) devices are now embedded in every part of our lives, with more and more devices becoming connected to the internet each day. This is a trend that can trace its origins back to the start of the 1990s wherein a toaster was created by John Romkey that could be turned on and off over the internet. This demonstrated what could potentially be achieved with everyday household appliances. Today, IoT devices are in nearly every electronic device we use and with IBM’s announcement in 2018 that they had made the smallest computer in the world measuring 1 millimetre by 1 millimetre, there is almost nothing an IoT device can’t fit into.
Read More
Topics:
Cyber Security,
Nettitude,
News,
Security Blog,
Cyber Security Blog,
Download Area,
SEO Series
By Nettitude
For many years, aerospace and aviation security has been primarily focused on the physical aspects of maintaining safety; from airside safety checks to ensure unauthorised personnel cannot access critical areas, to airport safety measures that ensure the safety of passengers and crew on board the plane. However, as passenger convenience and safety has advanced, as well as increased connectivity between airports, aboard a plane, and the outside world, the previous security model has become obsolete.
In line with this, we have recently seen the introduction of CAA ASSURE, a new cybersecurity audit model for third parties providing services to the Aerospace industry. Find out in the below post about what ASSURE entails and what Nettitude can offer in relation to this.
Read More
Topics:
Cyber Security,
Nettitude,
News,
Security Blog,
Cyber Security Blog,
Download Area
By Graham Sutherland, Senior Vulnerability Researcher
Developing and implementing secure remote access solutions can be a challenge in itself. As new threats continue to emerge and existing threats evolve, ensuring both your physical communications infrastructure and your communications operations are secure is vital to the day to day operations of your business. However, when factoring in the challenges of remote communications at sea, things can begin to get even more tricky if you don’t follow the correct procedures for establishing secure methods of remote communication.
At sea, the two main challenges are the availability of resources and connectivity. These two factors have over the past decade have been the driving force for the continual development of remote access solutions. Whilst today, we are in one of the best positions to defend our assets against ongoing threats, there are still an extensive set of considerations to be made when evaluating an approach or vendor offering.
Below, we will outline 9 key considerations which must be made when implementing remote access communications.
Read More
Topics:
Cyber Security,
Nettitude,
News,
Security Blog,
Cyber Security Blog,
Download Area
By Mike Buckley at LRQA Nettitude
Effective network design is crucial for the smooth running of every business. As the heart of your business activity, your network is relied upon day-in, day-out by your staff to keep business flowing, and customers returning. As most of us have experienced before, when the network goes down, chaos usually follows. When this happens, it can often be a mammoth task to get everything back up and running and the time lost is irreplaceable. However, by following best practice for network design and configuration from the beginning, you could prevent many issues before they arise.
Below, we’ll explain why establishing a well-designed and configured network is important, as well as detailing the six factors that are essential to the smooth running of your network…
Read More
Topics:
Cyber Security,
Nettitude,
News,
Security Blog,
Cyber Security Blog,
Download Area,
SEO Series
By Nettitude
In the nearly fifteen years since Amazon launched its initial cloud computing offering, the ways we develop, deploy and manage applications have been changing at pace. More businesses are finding that the transition away from traditional data centre technology is offering advantages such as increased flexibility, more rapid time-to-market, and allowing them to scale to meet customer demand.
Of course, many of the security considerations of using cloud infrastructure mirror those for more traditional infrastructure, and organisations should draw on existing expertise to manage them. However, different ways of working in the cloud mean that there are new aspects to consider to ensure that you are secured against the latest threats. It’s also worth remembering that these new ways of working can also offer an opportunity to adopt more secure ways of working at a lower cost – but only if deployed effectively.
Below, we’ll take a look at the main advantages of adopting cloud technology, as well as four key considerations your business should take.
Read More
Topics:
Cyber Security,
Nettitude,
News,
Security Blog,
Security Testing,
Cyber Security Blog,
Download Area,
Research & Innovation
By Graham Sutherland, Senior Researcher & Consultant at Nettitude
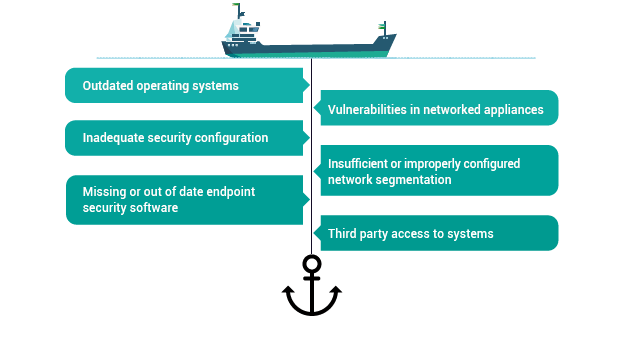
Modern ships utilise networked technologies in order to provide faster, more accurate, and more convenient operations of the vessel. This connectivity unfortunately brings with it new threats to the security of the vessel, its crew, and its cargo, while additionally bringing unique challenges in terms of systems maintenance.
Whilst the benefits of these technologies bring huge value to day to day operations, there are certain precautions which should be taken to offset any risks associated with integrating such technologies. Below are some of the most common security issues faced on today’s ships that you should be aware of.
Read More
Topics:
Cyber Security,
Nettitude,
News,
Security Blog,
Security Testing,
Cyber Security Blog,
Download Area,
Research & Innovation,
Marine and Offshore