By Nettitude
We are pleased to announce, Nettitude will be exhibiting at the 20th PCI London event this month at Park Plaza, Victoria. The annual PCI events are well known for delivering the latest industry insights, updates and keynote talks on all things PCI-DSS, and are not to be missed by anyone working within the industry.
Read More
Topics:
Cyber Security,
Nettitude,
Events,
News,
Security Blog,
Security Testing,
Cyber Security Blog
The shipping sector has traditionally stood apart from the developments in cybersecurity over the past decade. With the majority of critical functions and assets physically isolated by miles of ocean, the need to secure these resources against cyber threats has seemed similarly remote.
However, in recent years, this hands-off approach to cybersecurity and assurance has become riskier and ultimately, costlier. In the modern cyber threat landscape, less capable adversaries such as hacktivists and teenage virus writers take a back seat to organised criminals and even nation state-sponsored threat actors. The cyber-crime economy is now mature, well-established, and well-developed.
Below we will take a look at the key learnings for ship owners and operators which can be taken from previous research and attacks, most notably the NotPetya attack in 2017 which caused major implications for global shipping giant Maersk.
Read More
Topics:
Cyber Security,
Nettitude,
News,
Security Blog,
Security Testing,
Cyber Security Blog,
Download Area,
Research & Innovation,
Marine and Offshore
By Graham Sutherland, Senior Vulnerability Researcher
The traditional online attack surface for ships is changing. Gone are the years where vessels were put to sea for months at a time with little or no contact made with the shore, with letters awaiting them at their next arrival port and unpredictable journey times and locations.
Even with the advent of satellite phones, GPS tracking and computer-based navigation, a typical ship will still have a much more limited online presence compared to shore-based organisations. However, this is changing rapidly. As the availability and reliability of internet connections aboard ships improves, it is natural that organisations will seek to leverage this connectivity for the purposes of remote monitoring and diagnostics.
Below, we take a look at the new and enhanced risks posed by remote access communication on board ships and how we can approach a safer way of operating to protect the ship, its assets and the people on board.
Read More
Topics:
Cyber Security,
Nettitude,
News,
Security Blog,
Security Testing,
Cyber Security Blog,
Download Area,
Research & Innovation,
Marine and Offshore
The explosive growth in communications services over the last two decades has dramatically changed the way that businesses operate in all sectors, improving efficiency and providing new opportunities. In the maritime sector, we can see this from the original adoption of VHF a hundred years ago for ship communication through to more recent safety technologies such as AIS and satellite communication. However, the limited bandwidth and high cost of these technologies has historically limited the sector’s ability to leverage them in many of the ways seen in other industries.
Notably, when adding new technologies or capabilities to existing systems, it’s important to consider any additional risk that may be presented; this can be both from vulnerabilities in the underlying technologies themselves, or from the way in which they can interact with or expose other capabilities. Where risks are identified, mitigations should be put in place to reduce them to an acceptable level. Below we explore some of the ways in which this can be done, and some examples of widely used maritime technologies.
Read More
Topics:
Cyber Security,
Nettitude,
News,
Security Blog,
Security Testing,
Cyber Security Blog,
Download Area,
Research & Innovation,
Marine and Offshore
We are pleased to announce the addition of Mike Hubbard, our new Security and Network Solutions (SNS) Account Manager, within the Security and Network Solutions team. This new team delivers network consultancy, enterprise network solutions and network security solutions. Throughout the forthcoming months, Mike will be working closely with our clients to assess the effectiveness of their current environments and advise on any appropriate action to ensure their business infrastructure and network solutions are as safe and effective as possible. Below is a further insight into how Mike will be working within this new team.
Read More
Topics:
Cyber Security,
Security Blog,
Cyber Security Blog
By Ben Densham, CTO at Nettitude
By 2021, Forbes estimates that there will be $6 trillion in damages caused by cyberattacks, a figure that exceeds the cost of all natural disasters in an entire year. However, cyberattacks and the impact they can have on organisations are now becoming much better understood, and more businesses are putting protocols and cybersecurity strategies in place to become proactive rather than reactive to cyber threats.
Creating a cybersecurity strategy involves working out what ‘good’ looks like for your business in terms of maintaining digital security, keeping cyber threats at bay and having a plan of action in place for the possibility of a breach. Your cybersecurity strategy should be a clear vision that’s well-articulated, has board-level engagement and is relevant to your industry. Whilst many businesses have a cybersecurity policy, this is no longer enough. It’s crucial to have a full strategy in place which instigates cultural change within your business ecosystem and isn’t just reactive to threats but proactively ensures your business is doing everything possible to protect itself from cyberattacks.
Here are 5 steps to consider when creating your effective cybersecurity strategy:
.
Read More
Topics:
Cyber Security,
Nettitude,
News,
Security Blog,
Security Testing,
Cyber Security Blog,
Download Area,
Research & Innovation
We are pleased to announce the addition of Sarah Beresford, our new Security and Network Solutions Account Manager, within the Security and Network Solutions team. This new team delivers network consultancy, enterprise network solutions and network security solutions. Throughout the forthcoming months, Sarah will be working closely with our clients to assess the effectiveness of their current environments and advise on any appropriate action to ensure their business infrastructure is as safe as possible. Below is a further insight into how Sarah will be working within this new team.
Read More
Topics:
Cyber Security,
Nettitude,
News,
Security Blog,
Security Testing,
Cyber Security Blog,
Download Area,
Research & Innovation
By Joel Snape, Senior Security Researcher at Nettitude
Across most branches of industry, it is common to find security companies doing pro-active vulnerability research on equipment used in that industry and publishing details of the issue found after liaising with the vendor to ensure they are fixed. For example, in the wake of several large-scale internet attacks in 2016, researchers focused their attention on IoT devices with many reports surfacing of issues with devices such as CCTV cameras, home routers and network-connected storage devices.
In the maritime space, however, much less research has been publicly shared, predominantly because of the comparative cost and lack of accessibility of standard maritime equipment, although research has been carried out for several years, and some of the results have been publicly presented. Nettitude have pulled together highlights of the most relevant research in the public domain from a few key systems and highlighted the impact these vulnerabilities have within the marine and offshore sector, full details of which can be found in this report. So, what did the researchers find? Is the equipment currently used secure?
Read More
Topics:
Cyber Security,
Nettitude,
News,
Security Blog,
Security Testing,
Cyber Security Blog,
Download Area,
Research & Innovation
By Joel Snape, Senior Research Analyst at Nettitude
Being able to get accurate location information anywhere in the world is something we have come to take for granted. The ready availability of receivers means that Global Navigation Satellite Systems (GNSS) have been adopted across sectors in ways that were never envisaged when the first Global Positioning System (GPS) NAVSTAR 1 satellite was launched in 1978. From tracking sports players on a pitch for improved training to enabling precision agriculture for enhanced crop yields, being able to quickly and cost-effectively obtain accurate location information has enabled significant innovation.
Read More
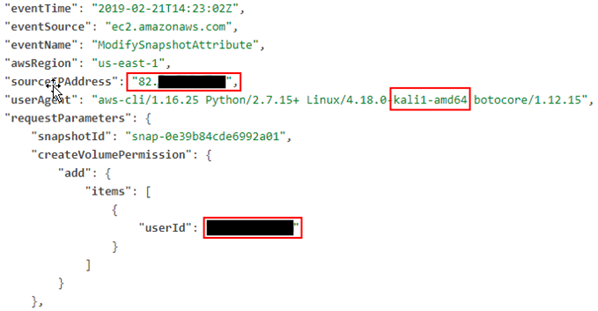
By Iraklis Mathiopoulos, Managing Principal Security Consultant at Nettitude
October is Cyber Security Awareness Month, which is a great opportunity for companies and individuals to review and improve their cyber security processes and knowledge. At Nettitude, we will be releasing a new blog post every week of Cyber Security Awareness Month on our latest cyber security research, as well as our insights on the latest industry news and trends. We hope you’ll find them helpful, and as always please contact us with any questions.
+++
As cloud infrastructure has become common, it has also become common for penetration testers to find themselves attacking clients that rely on AWS or Azure environments, for example, for handling, storing, and processing critical data.
There are many new and interesting attack paths an adversary can take once they have obtained some sort of access to the environment.
Read More
Topics:
Cyber Security Blog,
Research & Innovation