October 2021 saw our vulnerability research team uncover a Microsoft vulnerability dating back 14 years. In the wrong hands, it would have caused untold damage to businesses reliant on Microsoft’s VPN.
Nettitude
Recent Posts
Topics: Microsoft Bug, Microsoft VPN, Denial of Service, DoS, CVE-2022-23253, Vulnerability Research
Cybersecurity Training for Employees: How to Safeguard Your Organisation | Nettitude
While your business might have the latest technology to safeguard its private information, the reality is that your employees may be the weakest link in your organisation when it comes to cybersecurity. In fact, human error is still widely considered the number one cause of cybersecurity breaches.
So, what can you do to ensure your employees don’t make mistakes? The most straightforward approach is a detailed cybersecurity training course that educates employees on spotting common threats.
Here, we highlight some of the best places to start when teaching your employees about how they can avoid becoming a victim of a cyber-attack.
Topics: cyber security training and certification, cybersecurity training courses, cyber security training courses hong kong, cyber security singapore, cyber security risk management process, cyber risk management strategy, cybersecurity training in singapore
4 Ways to Detect Phishing Attempts: Email Protection 101 | Nettitude
Phishing has been around since the early days of the Internet, but it remains a major thorn for businesses and individuals. These deceptive emails attempt to trick users with harmful attachments and misleading links, using convincing promises, requests or anxiety-inducing news that leads people to not think clearly.
While you might think you can spot a phishing email from a mile away, the FBI’s Internet Crime Complaint Center (IC3) found that more than 240,000 people fell victim in the United States alone in 2020. Whether you need to protect yourself or educate your employees against cybersecurity risks, consider these tips to detect phishing attempts that land in your inbox.
Topics: cyber security services, cyber security consulting, certified information security consultant, cyber security consulting services, cyber security consultant
Firewalls are designed to form a protective barrier between your internal systems and untrusted outside networks. However, you must be certain that this part of your IT infrastructure has been installed and configured correctly. Otherwise, you risk malware being inserted or valuable data being stolen from your private systems.
This is where rigorous firewall penetration testing comes in. These simulated cyber-attacks locate, investigate and test for vulnerabilities from both outside intruders and internal threats. This way, your company will know where its weaknesses exist and have a plan to address any cybersecurity concerns.
Topics: Penetration Testing, firewall penetration testing, firewall penetration testing services, cyber security penetration testing, cybersecurity penetration testing, penetration test hong kong, firewall, penetration test, pentesting
Ransomware attacks are on the rise. Whether you’re a small business or a large organisation, you’re at risk and ransomware prevention is always better than recovering after an attack.
Topics: ransomware
What is the Log4Shell Vulnerability and how can you protect against it?
What is the Log4Shell Vulnerability?
Log4j is a logging library written in Java and the vulnerability, CVE-2021-44228, also commonly known as Log4Shell, allows a remote actor to send a crafted HTTP packet to servers or other software suite exposed to the internet, running the version below Log4j 2.15.0.
Topics: Log4Shell
It’s impossible to totally eliminate the risk of a cyberattack. No reputable cybersecurity company could give that assurance. For the same reason, you cannot simply pass or fail a TIBER test.
In fact, it would pose a higher risk to state you’d passed as you might take no further action.
Complacency in cybersecurity is risky.
Protecting your organisation from cyberattacks should be continual. And it must be specific to your risk profile and particular operations. As attacks become more sophisticated, so must your testing to keep one step ahead.
Topics: Financial Services, TIBER
By Vanessa Santos | Security Consultant at LRQA Nettitude
Json Web Tokens (JWTs) are commonly used in many applications to validate the client’s identity. The JWT token is provided during authentication in case of success and this is then used in all authenticated interactions to the application.
The validation of user’s identity is based on the user’s information stored in the JWT token which is signed by the server using JSON Web Signatures. The information exchanged within the JWT can also be encrypted using JSON Web Encryption however this is not widely used.
Although the JWT token can be used in web applications there is a number of caveats that come with the choice of implementing JWT authentication tokens that can result in them being hijacked.
In this article we will be discussing these security implementation issues and will uncover ways of preventing an attacker from hijacking JWT tokens.
Topics: Cyber Security, Nettitude, Security Blog, JSON Web Token
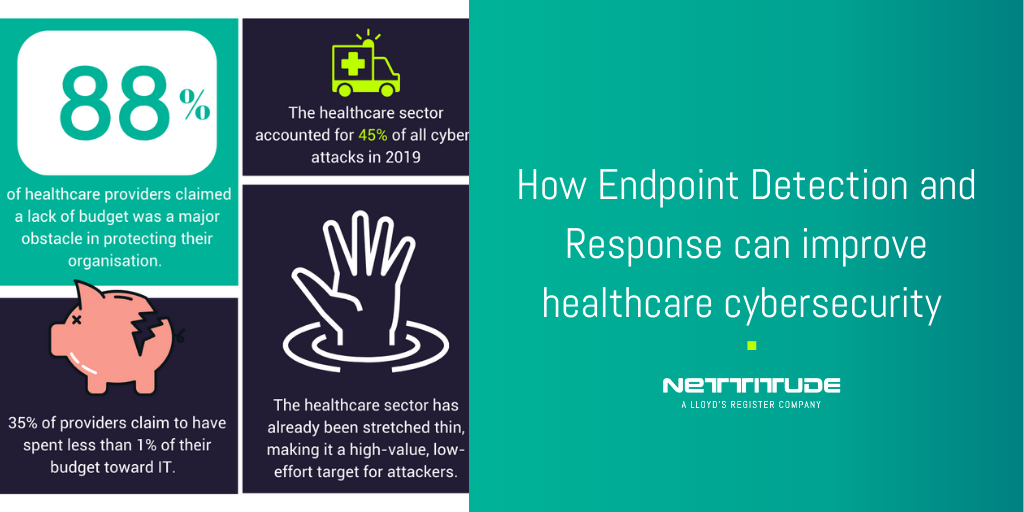
How Endpoint Detection and Response can improve healthcare cybersecurity | Nettitude
By Jenny Wu | Senior Incident Response Consultant at Nettitude
The move to the Cloud and remote working models has changed the way networks are connected. Today, we are shifting focus from security to protecting assets rather than the traditional perimeter. Traditional anti-virus is no longer able to keep up with newer attacks and vulnerabilities, allowing compromises to occur more frequently; especially for the healthcare industry which is frequently targeted. They therefore need additional protection in the form of Endpoint Detection and Response (EDR) Tooling.
Topics: Cyber Security, Nettitude, Security Blog, Financial Services, Financial Security
By Nettitude
Today, we’re excited to announce the launch of our Nettitude Bug Bounty programme .
Over the past few months, we’ve been running a Bug Bounty trial with a number of our clients, which we’re pleased to say has been successful. Now, we’re ready to open our Bug Bounty service up to the world.
Topics: Cyber Security, Nettitude, Security Blog