By Iraklis Mathiopoulos, Managing Principal Security Consultant at Nettitude
October is Cyber Security Awareness Month, which is a great opportunity for companies and individuals to review and improve their cyber security processes and knowledge. At Nettitude, we will be releasing a new blog post every week of Cyber Security Awareness Month on our latest cyber security research, as well as our insights on the latest industry news and trends. We hope you’ll find them helpful, and as always please contact us with any questions.
+++
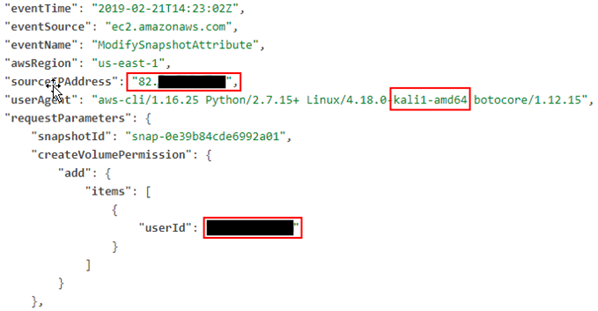
As cloud infrastructure has become common, it has also become common for penetration testers to find themselves attacking clients that rely on AWS or Azure environments, for example, for handling, storing, and processing critical data.
There are many new and interesting attack paths an adversary can take once they have obtained some sort of access to the environment.