With the digital era being well upon us, today’s state of affairs in the cybersecurity world has grown rather complex, and there are no exceptions for those of us who work in pen testing. Whilst traditional penetration testing techniques are still very much relevant to today’s reality, there’s no denying that there are many new tools, techniques and even new responsibilities that make penetration testing, on the whole, a mammoth task. In light of this, it becomes increasingly difficult for human teams to stay on top of these requirements effectively, and it’s becoming more and more necessary to lean on technological automation to support our cybersecurity endeavours.
An insight into how Artificial Intelligence is used in Penetration Testing
Topics: Cyber Security, Nettitude, Security Blog, Security Testing, Cyber Security Blog, Download Area, SEO Series
By Mike Buckley | Presales Security Consultant at Nettitude
What is an Endpoint
Firstly, what is an endpoint? An endpoint is usually a device which communicates with the network to which it is connected. This can be a myriad of devices including, laptops, mobiles, tablets, servers etc. As the attack vectors vary hugely depending on where we focus, this blog will primarily target the laptop/desktop world. Risks to all endpoints may be similar, but the mitigations are very different.
Topics: Cyber Security, Nettitude, Security Blog, Security Testing, Cyber Security Blog, Download Area, risk assessment, SEO Series, endpoint protection, endpoint security, endpoint protection software
By Mike Buckley | Presales Security Consultant at Nettitude
There are a few important principles that should be keeping a responsible CIO/CISO awake at night. Most certainly, one of those would be the loss or leakage of business-critical data such as customer Personal Identifiable Information (PII) or financial details. One of the primary functions of their role is to recognise this and put into place processes and technical controls to lower the risk of that data being exposed. We only have to look in the media to see numerous examples of data breaches. Threat actors as we now call them have been trying to access data of various kinds stretching back into the 1980s when modems connected everything together. Unfortunately for the CIO/CISOs of today there are compliance frameworks such as GDPR which firmly put the burden of responsibility on their shoulders.
Topics: Cyber Security, Nettitude, Security Blog, Security Testing, Cyber Security Blog, Download Area, risk assessment, SEO Series, data protection solutions, data loss protection, data leakage protection
Cybersecurity and the Cloud Series – 4 key considerations to take when adopting cloud technology | Nettitude
By Nettitude
In the nearly fifteen years since Amazon launched its initial cloud computing offering, the ways we develop, deploy and manage applications have been changing at pace. More businesses are finding that the transition away from traditional data centre technology is offering advantages such as increased flexibility, more rapid time-to-market, and allowing them to scale to meet customer demand.
Of course, many of the security considerations of using cloud infrastructure mirror those for more traditional infrastructure, and organisations should draw on existing expertise to manage them. However, different ways of working in the cloud mean that there are new aspects to consider to ensure that you are secured against the latest threats. It’s also worth remembering that these new ways of working can also offer an opportunity to adopt more secure ways of working at a lower cost – but only if deployed effectively.
Below, we’ll take a look at the main advantages of adopting cloud technology, as well as four key considerations your business should take.
Topics: Cyber Security, Nettitude, News, Security Blog, Security Testing, Cyber Security Blog, Download Area, Research & Innovation
By Graham Sutherland, Senior Researcher & Consultant at Nettitude
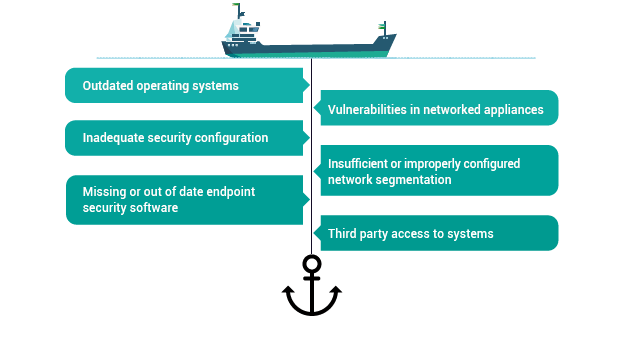
Modern ships utilise networked technologies in order to provide faster, more accurate, and more convenient operations of the vessel. This connectivity unfortunately brings with it new threats to the security of the vessel, its crew, and its cargo, while additionally bringing unique challenges in terms of systems maintenance.
Whilst the benefits of these technologies bring huge value to day to day operations, there are certain precautions which should be taken to offset any risks associated with integrating such technologies. Below are some of the most common security issues faced on today’s ships that you should be aware of.
Topics: Cyber Security, Nettitude, News, Security Blog, Security Testing, Cyber Security Blog, Download Area, Research & Innovation, Marine and Offshore
By Nettitude
We are pleased to announce, Nettitude will be exhibiting at the 20th PCI London event this month at Park Plaza, Victoria. The annual PCI events are well known for delivering the latest industry insights, updates and keynote talks on all things PCI-DSS, and are not to be missed by anyone working within the industry.
Topics: Cyber Security, Nettitude, Events, News, Security Blog, Security Testing, Cyber Security Blog
NotPetya Ransomware Attack on Maersk – Key Learnings | LRQA Nettitude
The shipping sector has traditionally stood apart from the developments in cybersecurity over the past decade. With the majority of critical functions and assets physically isolated by miles of ocean, the need to secure these resources against cyber threats has seemed similarly remote.
However, in recent years, this hands-off approach to cybersecurity and assurance has become riskier and ultimately, costlier. In the modern cyber threat landscape, less capable adversaries such as hacktivists and teenage virus writers take a back seat to organised criminals and even nation state-sponsored threat actors. The cyber-crime economy is now mature, well-established, and well-developed.
Below we will take a look at the key learnings for ship owners and operators which can be taken from previous research and attacks, most notably the NotPetya attack in 2017 which caused major implications for global shipping giant Maersk.
Topics: Cyber Security, Nettitude, News, Security Blog, Security Testing, Cyber Security Blog, Download Area, Research & Innovation, Marine and Offshore
Remote Access Solutions | Part 1 - An overview of remote solutions at sea | Nettitude
By Graham Sutherland, Senior Vulnerability Researcher
The traditional online attack surface for ships is changing. Gone are the years where vessels were put to sea for months at a time with little or no contact made with the shore, with letters awaiting them at their next arrival port and unpredictable journey times and locations.
Even with the advent of satellite phones, GPS tracking and computer-based navigation, a typical ship will still have a much more limited online presence compared to shore-based organisations. However, this is changing rapidly. As the availability and reliability of internet connections aboard ships improves, it is natural that organisations will seek to leverage this connectivity for the purposes of remote monitoring and diagnostics.
Below, we take a look at the new and enhanced risks posed by remote access communication on board ships and how we can approach a safer way of operating to protect the ship, its assets and the people on board.
Topics: Cyber Security, Nettitude, News, Security Blog, Security Testing, Cyber Security Blog, Download Area, Research & Innovation, Marine and Offshore
Cyber Risks in Communication Systems Series: Integration risks to communications technology for the M+O sector | Nettitude
The explosive growth in communications services over the last two decades has dramatically changed the way that businesses operate in all sectors, improving efficiency and providing new opportunities. In the maritime sector, we can see this from the original adoption of VHF a hundred years ago for ship communication through to more recent safety technologies such as AIS and satellite communication. However, the limited bandwidth and high cost of these technologies has historically limited the sector’s ability to leverage them in many of the ways seen in other industries.
Notably, when adding new technologies or capabilities to existing systems, it’s important to consider any additional risk that may be presented; this can be both from vulnerabilities in the underlying technologies themselves, or from the way in which they can interact with or expose other capabilities. Where risks are identified, mitigations should be put in place to reduce them to an acceptable level. Below we explore some of the ways in which this can be done, and some examples of widely used maritime technologies.
Topics: Cyber Security, Nettitude, News, Security Blog, Security Testing, Cyber Security Blog, Download Area, Research & Innovation, Marine and Offshore
By Ben Densham, CTO at Nettitude
By 2021, Forbes estimates that there will be $6 trillion in damages caused by cyberattacks, a figure that exceeds the cost of all natural disasters in an entire year. However, cyberattacks and the impact they can have on organisations are now becoming much better understood, and more businesses are putting protocols and cybersecurity strategies in place to become proactive rather than reactive to cyber threats.
Creating a cybersecurity strategy involves working out what ‘good’ looks like for your business in terms of maintaining digital security, keeping cyber threats at bay and having a plan of action in place for the possibility of a breach. Your cybersecurity strategy should be a clear vision that’s well-articulated, has board-level engagement and is relevant to your industry. Whilst many businesses have a cybersecurity policy, this is no longer enough. It’s crucial to have a full strategy in place which instigates cultural change within your business ecosystem and isn’t just reactive to threats but proactively ensures your business is doing everything possible to protect itself from cyberattacks.
Here are 5 steps to consider when creating your effective cybersecurity strategy:
.
Topics: Cyber Security, Nettitude, News, Security Blog, Security Testing, Cyber Security Blog, Download Area, Research & Innovation